Record, analyze, and manage event data from a single, centralized platform
Introducing OpenLM Audit System
Gain complete visibility into system activities. Track who did what, ensure compliance, and proactively detect threats using a unified, searchable event log.
Resolve issues with centralized insights
Stop chasing errors across different systems. Automatically capture and organize event data from all your OpenLM applications in one interface, so you can diagnose and fix problems instantly.
Core features of OpenLM Audit System

Data security
- Encryption and anonymization: Encrypt log data during transmission and storage. Additionally, anonymize personal data within the logs to enhance privacy and meet data protection requirements.
- Log retention, archiving, and destruction: Define policies for log retention, archiving, and destruction based on regulatory and operational needs. OpenLM Audit also supports automated log rotation, archival to long-term storage, and secure deletion of expired logs.
Log analysis
- Customizable logging: Customize logging parameters, specifying the events to log and the desired logging period.
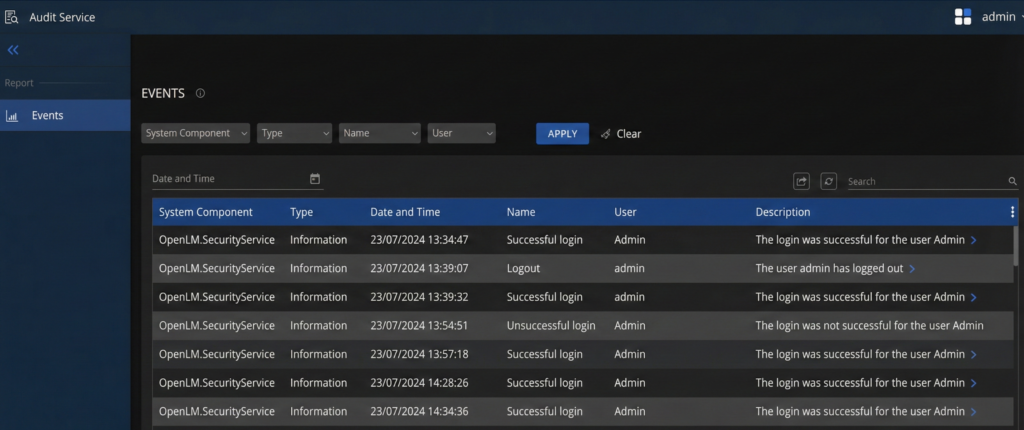
- Audit trails: Access detailed audit trails of critical activities within OpenLM applications and customer systems. This includes user logins, data modifications, configuration changes, and administrative actions.
- Access logs: Get comprehensive access logs, including details such as login attempts, session durations, IP addresses, and authentication methods.
- Data modification logging: Track all data modifications, including the creation, deletion, or update of records or files. This data will include information about the user, the type of modifications performed, and the specific data affected.
- Security incident logging: Record security-related events like failed login attempts, data exports, and changes in user privileges to aid in threat detection and mitigation.
- Compliance logging (For cloud solutions only): Implement robust logging mechanisms to track and ensure compliance with regulations like GDPR, CCPA, and SOC-2.

Log management
- Search and filtering: Leverage advanced search and filtering capabilities to quickly locate specific log entries based on various criteria.
- Alerts and notifications: Configure alert rules based on specific events or thresholds. The system sends notifications to designated personnel in case of unusual or suspicious activities.
Explore OpenLM Platform capabilities
Ready to dig deeper? Get the complete breakdown of all features of our new solution.

Frequently Asked Questions (FAQs)
What is the OpenLM Audit System?
The OpenLM Audit System is a comprehensive platform designed to record, analyze, and manage event data from various OpenLM applications and customer systems.
Why do I need the OpenLM Audit System?
You need the OpenLM Audit System to gain insights into system activities and potential security concerns through an easily accessible and well-structured log of events.
What are the core features of OpenLM Audit System related to data security?
The data security features include:
- Encryption and anonymization: Encrypts log data during transmission and storage, and anonymizes personal data within logs.
- Log retention, archiving, and destruction: Allows you to define policies for log retention, archiving, and destruction, and supports automated log rotation, archival, and secure deletion.
What are the core features of OpenLM Audit System related to log management?
Log management features include:
- Customizable logging: You can customize logging parameters, specifying events to log and the desired logging period.
- Audit trails: Access detailed audit trails of critical activities, including user logins, data modifications, configuration changes, and administrative actions.
- Access logs: Get comprehensive access logs with details like login attempts, session durations, IP addresses, and authentication methods.
- Data modification logging: Track all data modifications, including creation, deletion, or update of records, along with information about the user and type of modification.
- Security incident logging: Records security-related events such as failed login attempts, data exports, and changes in user privileges.
- Compliance logging (For cloud solutions only): Implements robust logging mechanisms to track and ensure compliance with regulations like GDPR, CCPA, and SOC-2.
How does OpenLM Audit System help with log analysis?
For log analysis, the system offers:
- Search and filtering: Advanced capabilities to quickly locate specific log entries based on various criteria.
- Alerts and notifications: Configure alert rules based on specific events or thresholds, sending notifications for unusual or suspicious activities.